Intro: A total of 13 people were found to have directly launched the cyberattacks, with more than 60 contracts signed to cover the malicious activities. The hackers used 41 tools to breach the firewalls, plant remote-controlled backdoors, steal critical data and erase the traces of doing so.
✓ They also tried to hide their real location and identity using so-called "jump servers." A total of 54 jump servers were traced by the investigators, which are spread in 17 countries like Japan, South Korea, Sweden, Poland and Ukraine.
Related
China Says US Hacked Aeronautics, Space Research University
China accused a US spy agency of hacking a government-funded university with aeronautics and space research programs, in Beijing’s latest effort to hit back at Washington’s complaints of cybersnooping.
NSA is accused of cyberattacks on Northwestern Polytechnical
China has been more direct in accusing US of conducting hacks
Updated
The National Security Agency’s Office of Tailored Access Operations carried out the attacks on Northwestern Polytechnical University in Xi’an, China’s National Computer Virus Emergency Response Center said in a statement. A team from the center and 360 Security Technology Inc. analyzed the university’s information systems after an attack from overseas was reported in June, the center added.
The NSA conducted more than 10,000 “vicious” cyberattacks on Chinese targets in recent years, collecting more than 140 gigabytes of data of “great value,” it said. The NSA and State Department declined to comment on the allegations.
Beijing and Washington have been engaged in an increasingly testy war of words over cyberspying, with China becoming more direct in naming American government agencies in its accusations. The US has sought to draw a distinction between operations it conducts for national security purposes and the industrial espionage it has accused China of waging against American companies.
Federal Bureau of Investigation Director Christopher Wray warned Western companies in July that China aims to “ransack” their intellectual property so it can eventually dominate key industries. Both countries previously agreed to not condone cybertheft of intellectual property or trade secrets during Chinese President Xi Jinping’s state visit to Washington in 2015.
Blacklists, Trade and More U.S.-China Flashpoints: QuickTake
Samantha Hoffman, a senior analyst at the Australian Strategic Policy Institute, said there has been an uptick in specific Chinese accusations of US cyberattacks and that the US should respond with specific details of Chinese actors engaged in espionage.
“The US and allies need to focus on explaining why China’s activity in this space is abnormal -- beyond what most intelligence agencies do,” she said. “Of course, China is likely to continue responding with similar accusations, which may or not be factual.”
China has in the past typically responded to such criticism by casting itself as a victim of hacking, dismissing the US an “empire of hackers” and pointing to former NSA contractor Edward Snowden’s revelations almost a decade ago about U.S. espionage. Among those were claims that the NSA had hacked into the computers of Tsinghua University, one of the China’s top research centers.
More recently, Beijing has shifted its strategy by directly accusing the US of cyberattacks and naming targets. In February, Chinese cybersecurity firm Pangu Lab said it discovered US-sponsored hacking activity in China: malware in domestic IT systems it claims was created by hacking group Equation, “generally believed” to be linked to the NSA.
The shift has been an effort to increase public awareness of US activities and to regain the diplomatic initiative globally from the US and its allies, which have for many years accused China of attacks, said Greg Austin, an expert in Chinese cyberactivities at the Singapore-based International Institute for Strategic Studies.
“It’s a change of direction and probably about almost 10 years overdue,” he said. “The disparity between what the United States government and its allies have released on China and what China has released on American and ally attacks is massive. We knew almost nothing from Chinese officials on the scale of American attacks.”
At the same time, the US and its allies have escalated their investments in espionage and surveillance on China and Russia, he said.
Chinese Report on Suspected NSA Hack Shows Beijing Pushing Back
State broadcaster China Central Television and other major state media outlets reported on the alleged hacks at Northwestern Polytechnical University, which is affiliated with the Ministry of Industry and Information Technology and runs research programs in aeronautics, astronautics and marine technology engineering.
The Communist Party’s Global Times newspaper also tweeted about the report and put it on its Weibo social media account. The news was among the top trending topics on Weibo on Monday, attracting 210 million views.
Police in Xi’an said in a statement in June that the university reported it had detected phishing emails that posed a “serious security threat” to critical databases.
— With assistance by Jing Li
(Updates with NSA and State Department declining to comment on the allegations.)
✓
U.S. hacked China 10,000 times, stole 140GB of critical data: Report
The U.S. National Security Agency (NSA) conducted over 10,000 cyberattacks against China in recent years and is suspected to have stolen 140 gigabytes of valuable data, according to a joint investigation report released on Monday by China's National Computer Virus Emergency Response Center (CVERC) and internet security company Qihoo 360 Technology Co. Ltd.
The investigation was launched after Northwestern Polytechnical University (NPU), a leading Chinese university in aviation, reported being hacked in April. The investigators have traced the cyberattacks back to the Office of Tailored Access Operations (TAO) of the NSA.
"NPU was targeted because many top-level talents in the country work there," Jin Qi, deputy head of the local police bureau, told China Media Group (CMG). "Many national-level research projects were conducted there."
A total of 13 people were found to have directly launched the cyberattacks, with more than 60 contracts signed to cover the malicious activities.
"They first scout the network," said Bian Liang, a network security expert at Qihoo 360. "Then they create customized tools to target the specific network."
The hackers used 41 tools to breach the firewalls, plant remote-controlled backdoors, steal critical data and erase the traces of doing so.
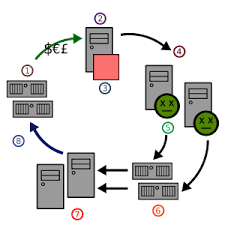
"There are four steps in their attack," said Du Zhenhua, senior engineer at the CVERC. "Break in, establish long-term control, keep stealing data and after everything's done, clear the scene."
They also tried to hide their real location and identity using so-called "jump servers." A total of 54 jump servers were traced by the investigators, which are spread in 17 countries like Japan, South Korea, Sweden, Poland and Ukraine.
The IP addresses used to control the jump servers are 209.59.36.*, 69.165.54.*, 207.195.240.* and 209.118.143.*.
Some of the jump servers were "zombie computers" hacked by the NSA without the knowledge of the owners. The hackers mostly target two "zero-day" vulnerabilities in the Solaris operating system developed by Sun Microsystems, which is now a part of U.S. tech giant Oracle Corporation.
The NSA tried to hide their identity by buying assets anonymously or through dummy companies like Jackson Smith Consultants and Mueller Diversified Systems. But investigators managed to trace their real identity.
"As long as we can sense the attacks," said Zhou Hongyi, founder of Qihoo 360. "We can clear them up, trace the origin and patch the loopholes."
The investigators said they will reveal more details of U.S. hacking and spying technologies in the future.
China's Ministry of Foreign Affairs has responded to the findings. Spokesperson Mao Ning told reporters that China strongly condemns such activities, adding that the U.S. side should stop the cyberattacks immediately.
"China wishes to work with the international community to keep the network safe," she said during a routine press briefing on Monday.
(Cao Qingqing contributed to the story.)
.jpg)
.jpg)
.jpg)

.jpg)
.jpg)
.jpg)


No comments:
Post a Comment