First this
Emotet botnet comeback orchestrated by Conti ransomware gang
The Emotet botnet is back by popular demand, resurrected by its former operator, who was convinced by members of the Conti ransomware gang
[...] Conti ransomware may rise to dominance
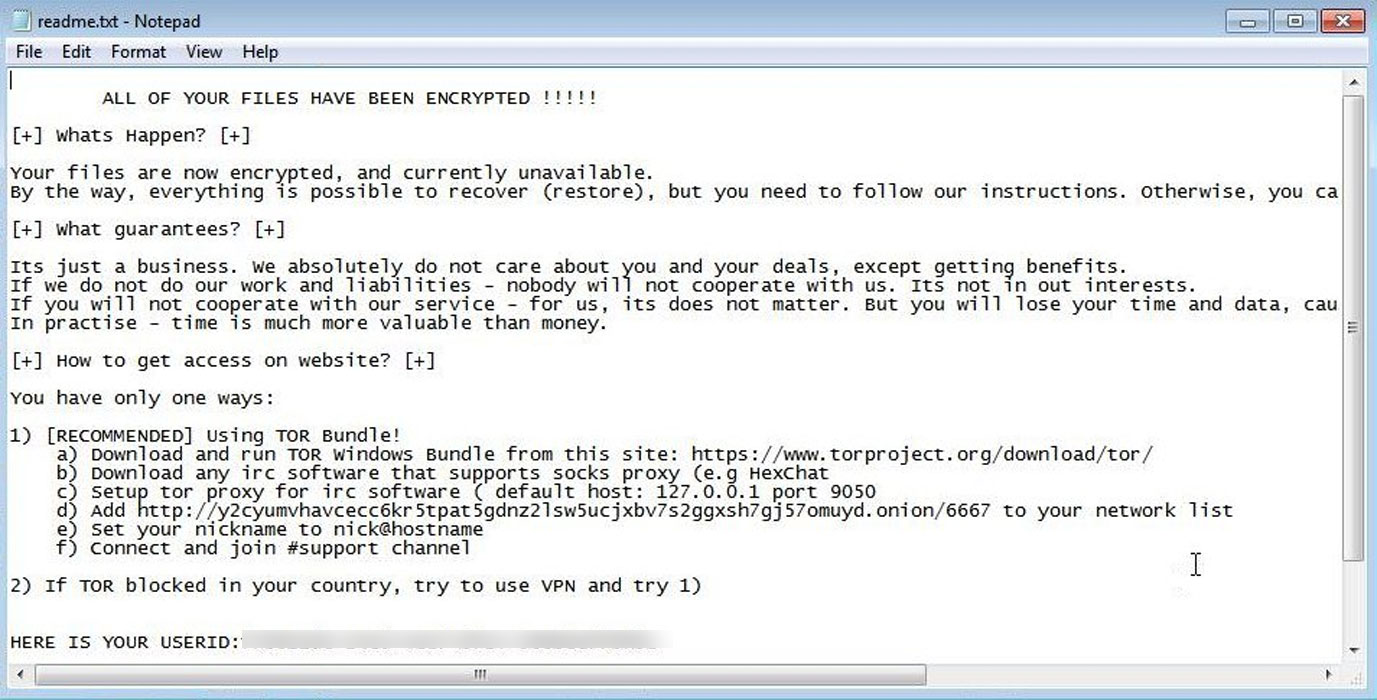
Considered the most widely distributed malware, Emotet acted as a malware loader that provided other malware operators initial access to infected systems that were assessed as valuable.
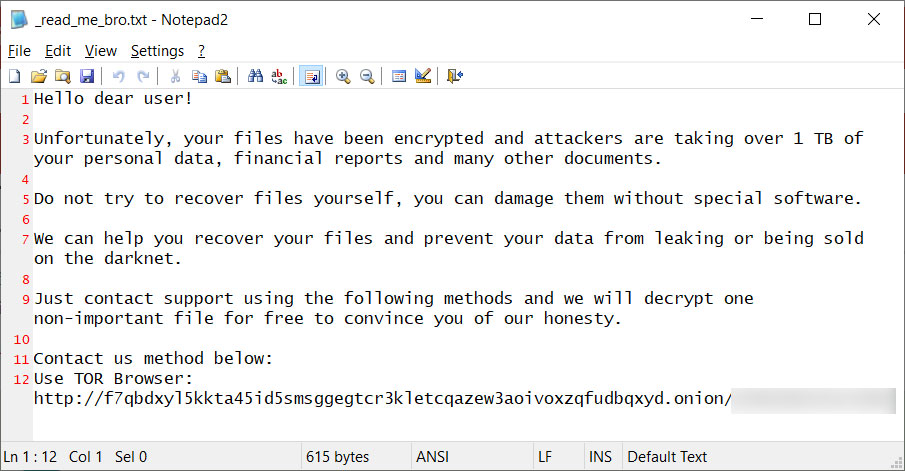
Qbot and TrickBot, in particular, were Emotet’s main customers and used their access to deploy ransomware (e.g. Ryuk, Conti, ProLock, Egregor, DoppelPaymer, and others).
____________________________________________________________________________________
“Emotet’s strategic, operational, and tactical agility was executed through a modular system enabling them to tailor payload functionality and specialization for the needs of specific customers”
- AdvIntel
____________________________________________________________________________________
The botnet operators provided initial access at an industrial scale, so many malware operations depended on Emotet for their attacks, especially those in the so-called Emotet-TrickBot-Ryuk triad.
Ryuk is the predecessor of Conti ransomware. The switch occurred last year when Conti activity started to increase and Ryuk detections dwindled down.
The operators of both ransomware strains have a long history of attacks hitting organizations in the healthcare and education sector. . . "
READ MORE

No comments:
Post a Comment