WHOA! Bleep! Bleep! + More Bleep-Bleeps
MediaMarkt hit by Hive ransomware, initial $240 million ransom
Electronics retail giant MediaMarkt has suffered a Hive ransomware with an initial ransom demand of $240 million, causing IT systems to shut down and store operations to be disrupted in Netherlands and Germany.
MediaMarkt is Europe's largest consumer electronics retailer, with over 1,000 stores in 13 countries. MediaMarkt employs approximately 53,000 employees and has a total sales of €20.8 billion.
A Hive ransomware attack
MediaMarkt suffered a ransomware attack late Sunday evening into Monday morning that encrypted servers and workstations and led to the shutdown of IT systems to prevent the attack's spread.
BleepingComputer has learned that the attack affected numerous retail stores throughout Europe, primarily those in the Netherlands. . .
BleepingComputer has confirmed that the Hive Ransomware operation is behind the attack and initially demanded a huge, but unrealistic, $240 million ransom demand to receive a decryptor for encrypted files.
Ransomware gangs commonly demand large ransoms at the beginning to allow room for negotiation and usually receive a fraction of the initial demand. However, in the attack on MediaMarkt, BleepingComputer has been told it was almost automatically reduced to a much lower amount.
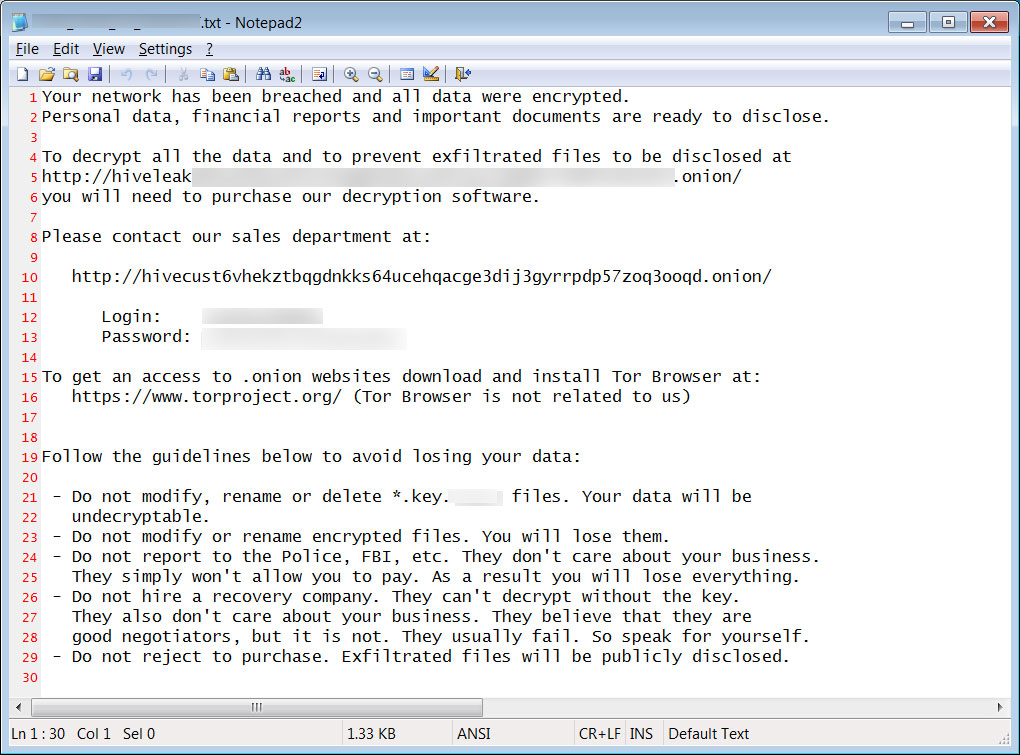
While it is not clear if unencrypted data has been stolen as part of the attack, Hive ransomware is known to steal files and publish them on their 'HiveLeaks' data leak site if a ransom is not paid.
When we reached out to MediaMarkt earlier today about the attack we received the following statement:
The MediaMarktSaturn Retail Group and its national organizations became the target of a cyberattack. The company immediately informed the relevant authorities and is working at full speed to identify the affected systems and repair any damage caused as quickly as possible. . .
Who is Hive ransomware?
Hive ransomware is a relatively new operation launched in June 2021 that is known to breach organizations through malware-laced phishing campaigns.
Once they gain access to a network, the threat actors will spread laterally through a network while stealing unencrypted files to be used in extortion demands.
When they gain admin access on a Windows domain controller, they deploy their ransomware throughout the network to encrypt all devices.
The ransomware gang is known to seek out and delete any backups to prevent them from being used by the victim to recover their data.
Hive has also created variants used to encrypt Linux and FreeBSD servers, commonly used to host virtual machines.
Unlike some ransomware operations that will not encrypt healthcare institutions, nursing homes, government agencies, and other essential services, Hive ransomware does not seem to care who they target.
In August, this was shown when Hive ransomware attacked the non-profit Memorial Health System, which forced staff to work with paper charts and disrupted scheduled surgeries.
Update 11/8/21 12:01 PM EST: Added statement from MediaMarkt.
Update 11/8/21 01:53 PM EST: Added information about Hive Ransomware.
State hackers breach defense, energy, healthcare orgs worldwide
"Cybersecurity firm Palo Alto Networks warned over the weekend of an ongoing hacking campaign that has already resulted in the compromise of at least nine organizations worldwide from critical sectors, including defense, healthcare, energy, technology, and education.
To breach the orgs networks, the threat actors behind this cyberespionage campaign exploited a critical vulnerability (CVE-2021-40539) in Zoho's enterprise password management solution known as ManageEngine ADSelfService Plus which allows remotely executing code on unpatched systems without authentication.
The attacks observed by Palo Alto Networks researchers started on September 17 with scans for vulnerable servers, nine days after the US Cybersecurity and Infrastructure Security Agency (CISA) warned it detected exploits used in the wild and one day after a joint advisory was published by CISA, the FBI, and the United States Coast Guard Cyber Command (CGCYBER).
Exploitation attempts began on September 22 after five days of harvesting info on potential targets who hadn't yet patched their systems.
"While we lack insight into the totality of organizations that were exploited during this campaign, we believe that, globally, at least nine entities across the technology, defense, healthcare, energy and education industries were compromised," the researchers said.
"Through global telemetry, we believe that the actor targeted at least 370 Zoho ManageEngine servers in the United States alone. Given the scale, we assess that these scans were largely indiscriminate in nature as targets ranged from education to Department of Defense entities."
Following the joint advisory, the researchers observed another series of unrelated attacks that failed to compromise their targets, hinting at other state-backed or financially-motivated hacking groups likely joining in to exploit companies using Zoho servers.
Right now, according to Palo Alto Networks' scans, there are over 11,000 internet-exposed servers running the vulnerable Zoho software — it's currently unknown how many of these systems have been patched.
Targets on credentials, persistence
After successfully getting a foothold on their victims' systems using CVE-2021-40539 exploits, the threat actors first deployed a malware dropper that delivered Godzilla web shells on compromised servers to gain and maintain access to the victims' networks, as well as malware, including an open-source backdoor known as NGLite.
They also used KdcSponge, malware known as credential stealer, which hooks into Windows LSASS API functions to capture credentials (i.e., domain names, usernames, and passwords) that later get sent to attacker-controlled servers.
"After gaining access to the initial server, the actors focused their efforts on gathering and exfiltrating sensitive information from local domain controllers, such as the Active Directory database file (ntds.dit) and the SYSTEM hive from the registry," the researchers found.
"Ultimately, the actor was interested in stealing credentials, maintaining access and gathering sensitive files from victim networks for exfiltration."
Attacks linked to Chinese APT27 state hackers
Even though the researchers are working on attributing these attacks to a specific hacking group, they suspect that this is the work of a Chinese-sponsored threat group known as APT27 (also tracked as TG-3390, Emissary Panda, BRONZE UNION, Iron Tiger, and LuckyMouse).
The partial attribution is based on malicious tools and tactics used in this campaign that match APT27's previous activity as a hacking group active since at least 2010 and targeting the same range of industry sectors (e.g., defense, technology, energy, aerospace, government, and manufacturing) in cyber espionage campaigns.
Palo Alto Networks' report also includes analysis from US Government partners, including NSA's Cybersecurity Collaboration Center, a component designed to prevent and block foreign cyber threats to National Security Systems (NSS), the Department of Defense, and the Defense Industrial Base (DIB) with the help of private industry partners.
In early March, APT27 was also linked to attacks exploiting critical bugs (dubbed ProxyLogon) to achieve remote code execution without authentication on unpatched on-premises Microsoft Exchange servers worldwide.
US and allies, including the European Union, the United Kingdom, and NATO, officially blamed China in June for this year's widespread Microsoft Exchange hacking campaign
===========================================
-
U.S. offers $10 million reward for leaders of REvil ransomware
The U.S. is offering up to $10 million for identifying or locating leaders in the REvil (Sodinokibi) ransomware operation, including $5 million leading to the arrest of affiliates.
- November 08, 2021
- 07:11 PM
 0
0
-
Robinhood discloses data breach impacting 7 million customers
Stock trading platform Robinhood has disclosed a data breach after their systems were hacked and a threat actor gained access to the personal information of approximately 7 million customers.
- November 08, 2021
- 04:40 PM
 0
0
-
Softbank plans to charge electronic gadgets using 5G antennas
Japanese tech giant SoftBank is planning to trial wireless charging of smartwatches and earbuds using power transmitted through 5G antennas.
- November 08, 2021
- 02:59 PM
 0
0
-
US sanctions Chatex cryptoexchange used by ransomware gangs
The US Treasury Department announced today sanctions against the Chatex cryptocurrency exchange for helping ransomware gangs evade sanctions and facilitating ransom transactions.
- November 08, 2021
- 01:26 PM
 0
0
-
US seizes $6 million from REvil ransomware, arrest Kaseya hacker
The United States Department of Justice today has announced charges against a REvil ransomware affiliate responsible for the attack against the Kaseya MSP platform on July 2nd and seizing more than $6 million from another REvil partner.
- November 08, 2021
- 01:18 PM
 0
0
-
Sitecore XP RCE flaw patched last month now actively exploited
The Australian Cyber Security Center (ACSC) is alerting web admins of the active exploitation of CVE-2021-42237, a remote code execution flaw in the Sitecore Experience Platform (Sitecore XP).
- November 08, 2021
- 11:56 AM
 0
0
-
Criminal group dismantled after forcing victims to be money mules
The Spanish police have arrested 45 people who are believed to be members of an online fraud group that operated twenty websites to defraud at least 200 people of 1,500,000 Euros ($1.73 million).
- November 08, 2021
- 10:40 AM
 0
0
-
REvil ransomware affiliates arrested in Romania and Kuwait
Romanian law enforcement authorities have arrested two suspects believed to be Sodinokibi/REvil ransomware affiliates, allegedly responsible for infecting thousands of victims.
- November 08, 2021
- 09:51 AM
 1
1
-
MediaMarkt hit by Hive ransomware, initial $240 million ransom
Electronics retail giant MediaMarkt has suffered a Hive ransomware with an initial ransom demand of $240 million, causing IT systems to shut down and store operations to be disrupted in Netherlands and Germany.
- November 08, 2021
- 09:27 AM
 0
0













No comments:
Post a Comment