A brief history of wipers
The documentation of Azov, Fantasy, and Sandals, comes days after researchers at security firm Kaspersky detailed CryWiper, a never-before-seen wiper that attacked courts and mayoral offices in Russia.
The wiper discoveries come as this form of destructive malware has grown increasingly common over the past decade. In 2012, a wiper known as Shamoon wreaked havoc on Saudi Arabia's Saudi Aramco and Qatar's RasGas. Four years later, a new variant of Shamoon returned and struck multiple organizations in Saudi Arabia.
In 2017, self-replicating malware Russia initially unleashed on Ukraine spread across the globe in a matter of hours. Known as NotPetya, the wiper caused an estimated $10 billion in damage, making it the most costly cyberattack in history. In the past year, a flurry of new wipers has appeared. They include DoubleZero, IsaacWiper, HermeticWiper, CaddyWiper, WhisperGate, AcidRain, Industroyer2, and RuRansom
Effective, fast, and unrecoverable: Wiper malware is popping up everywhere
Wiper malware from no fewer than 9 families has appeared this year. Now there are 2 more.
Getty Images
"Over the past year, a flurry of destructive wiper malware from no fewer than nine families has appeared. In the past week, researchers cataloged at least two more, both exhibiting advanced codebases designed to inflict maximum damage.
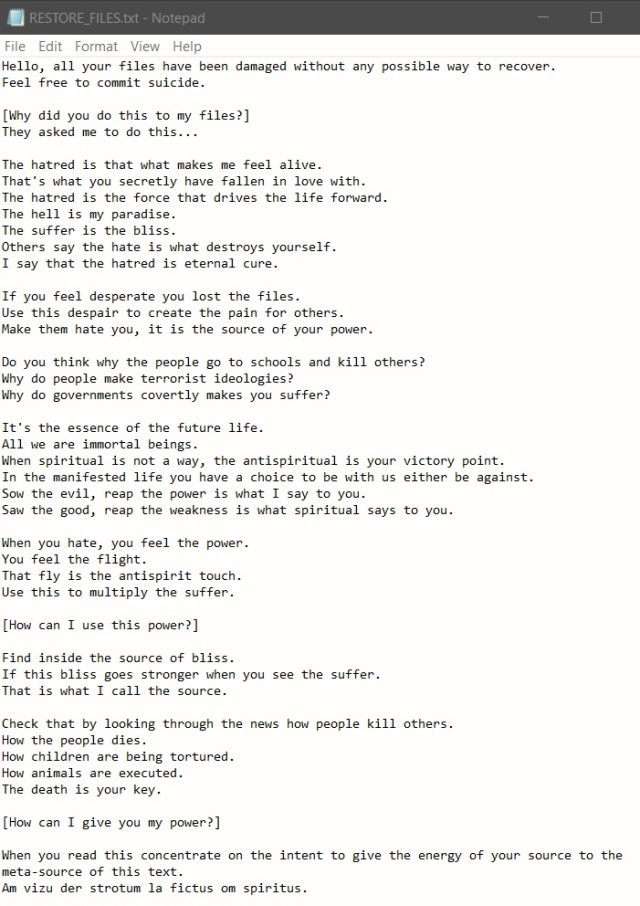
On Monday, researchers from Check Point Research published details
of Azov, a previously unseen piece of malware that the company
described as an “effective, fast, and unfortunately unrecoverable data
wiper.” Files are wiped in blocks of 666 bytes by overwriting them with
random data, leaving an identically sized block intact, and so on. The
malware uses the uninitialized local variable char buffer[666].
Script kiddies need not apply
After permanently destroying data on infected machines, Azov displays a note written in the style of a ransomware announcement. The note echoes Kremlin talking points regarding Russia’s war on Ukraine, including the threat of nuclear strikes. The note from one of two samples Check Point recovered falsely attributes the words to a well-known malware analyst from Poland.
Despite the initial appearance of an undertaking by juvenile developers, Azov is by no means unsophisticated. It’s a computer virus in the original definition, meaning it modifies files—in this case, adding polymorphic code to backdoor 64-bit executables—which attack the infected system. It’s also entirely written in assembly, a low-level language that’s extremely painstaking to use but also makes the malware more effective in the backdooring process. Besides the polymorphic code, Azov uses other techniques to make detection and analysis by researchers harder.
“Although the Azov sample was considered skidsware when first encountered (likely because of the strangely formed ransom note), when probed further one finds very advanced techniques—manually crafted assembly, injecting payloads into executables in order to backdoor them, and several anti-analysis tricks usually reserved for security textbooks or high-profile brand-name cybercrime tools,” Check Point researcher Jiri Vinopal wrote. “Azov ransomware certainly ought to give the typical reverse engineer a harder time than the average malware.”
A logic bomb built into the code causes Azove to detonate at a predetermined time. Once triggered, the logic bomb iterates over all file directories and executes the wiping routine on each one, except for specific hard-coded system paths and file extensions. As of last month, more than 17,000 backdoored executables had been submitted to VirusTotal, indicating that the malware has spread widely.
Last Wednesday, researchers from security firm ESET disclosed another previously unseen wiper they called Fantasy, along with a lateral movement and execution tool named Sandals. The malware was spread using a supply-chain attack that abused the infrastructure of an Israeli firm that develops software for use in the diamond industry. Over a 150-minute period, Fantasy and Sandals spread to the software maker’s customers engaged in human resources, IT support services, and diamond wholesaling. The targets were located in South Africa, Israel, and Hong Kong.
Fantasy heavily borrows code from Apostle, malware that initially masqueraded as ransomware before revealing itself as a wiper. Apostle has been linked to Agrius, an Iranian threat actor operating out of the Middle East. The code reuse led ESET to attribute Fantasy and Sandals to the same group.




 0
0



















No comments:
Post a Comment