Biz & IT / Information Technolog
#GermanyRIP. Kremlin-loyal hacktivists wage DDoSes to retaliate for tank aid
Killnet hacktivist group appears to have indirect ties to the Russian government.
"Threat actors loyal to the Kremlin have stepped up attacks in support of its invasion of Ukraine, with denial-of-service attacks hitting German banks and other organizations and the unleashing of a new destructive data wiper on Ukraine.
Germany's BSI agency, which monitors cybersecurity in that
country, said the attacks caused small outages but ultimately did little
damage.
“Currently, some websites are not accessible,” the BSI said in a statement to news agencies. “There are currently no indications of direct effects on the respective service and, according to the BSI's assessment, these are not to be expected if the usual protective measures are taken.”
The distributed denial-of-service attacks, typically called DDoSes, appeared to come as retaliation for the German government’s decision to allow its advanced Leopard 2 tanks to be supplied to Ukraine. Researchers at security firm Cado Labs said on Wednesday that Russian-language hacktivist groups—including one calling itself Killnet—issued calls for its members to wage DDoSes against targets in Germany. The campaign, which began on Tuesday as the Leopard 2 tank decision appeared immanent, used the hashtag #ГерманияRIP, which translates to “#GermanyRIP.”
Messages soon followed from other Russian-speaking groups claiming attacks against the websites of major German airports, including Hamburg, Dortmund, Dresden, and Dusseldorf; German development agency GIZ; Germany’s national police site; Deutsche Bank; and online payment system Giropay. It wasn’t clear if any of the attacks successfully shut down the sites.
Another group calling itself “Anonymous Sudan,” meanwhile, also claimed responsibility for DDoS attacks against the websites of the German foreign intelligence service and the Cabinet of Germany, in support of Killnet.
“As we’ve seen throughout the Russia-Ukraine war, cyber threat actors are quick to respond to geopolitical events, and are successful in uniting and mobilizing groups with similar motives,” Cado Labs researchers wrote. “The involvement of a group purporting to be the Sudanese version of Anonymous is interesting to note, as it demonstrates the ability for Russian-language hacktivist groups to conduct this mobilisation and collaboration on an international level.”
Killnet emerged shortly after Russia’s invasion of Ukraine. Last June, it took credit for what the Lithuanian government called “intense” DDoSes on the country’s critical infrastructure, including parts of the Secure National Data Transfer Network, which helps execute Lithuania's strategy for ensuring national security in cyberspace. Discussions on a Killnet Telegram channel at the time indicated the attacks were in retaliation for the Baltic government closing transit routes to Russia earlier that month.
In September, security firm Mandiant said it uncovered evidence that Killnet had indirect links to the Kremlin. Specifically, Mandiant researchers said Killnet coordinated some of its activities with a group called Xaknet and that Xaknet, in turn, had coordinated some activities with threat actors from the Russian Main Intelligence Directorate, or GRU.
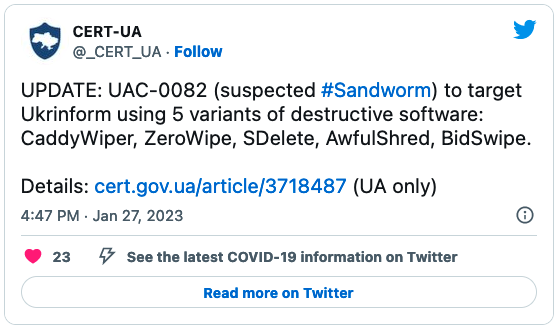
In related news, on Friday, researchers from security firm Eset reported that another Kremlin-backed threat actor, known as Sandworm, unleashed a never-before-seen data wiper on Ukrainian targets. The destructive malware, dubbed SwiftSlicer, is written in the Go programming language and uses randomly generated 4096-byte blocks to overwrite data."


No comments:
Post a Comment