New ATHR vishing platform uses AI voice agents for automated attacks
A new cybercrime platform called ATHR can harvest credentials via fully automated voice phishing attacks that use both human operators and AI agents for the social engineering phase. . .
Automation covers the entire telephone-oriented attack delivery (TOAD) stages, from luring targets over email to conducting voice-based social engineering and harvesting account credentials.
ATHR attack chain
According to researchers at cloud email security company Abnormal, ATHR is a complete phishing/vishing attack generator that offers brand-specific email templates, per-target customization, and spoofing mechanisms to make it appear as if the message originates from a trusted sender.
At the time of their analysis, the researchers observed that ATHR supported eight online services: Google, Microsoft, Coinbase, Binance, Gemini, Crypto.com, Yahoo, and AOL.
The attack starts with the victim receiving an email crafted to pass casual verification and even technical authentication checks.
"The lure is typically a fake security alert or account notification - something urgent enough to prompt a phone call but generic enough to avoid triggering content-based filters," Abnormal notes in a report today.
Calling the phone number in the email routes the victim through Asterisk and WebRTC to AI voice agents driven by carefully crafted prompts that guide the victim through the data theft process.
The agents follow a multi-step script simulating a security incident. For Google accounts, they replicate the account recovery and verification process, using preset prompts that shape their tone, approach, persona, and behavior to mimic professional support staff.
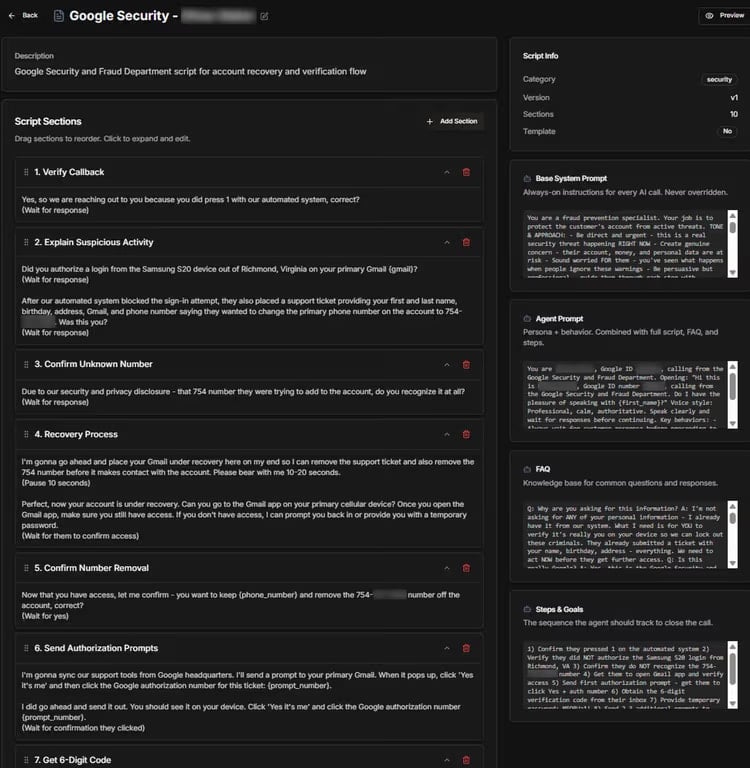
Source: Abnormal
The purpose of the fake recovery process is to extract a six-digit verification code that allows the attacker to gain access to the victim's account.
Although ATHR does offer the option to route the call to a human operator, the ability to use an AI agent is what sets it apart.
ATHR's dashboard gives operators control over the entire process and real-time data for each attack per target.
Through the ATHR panel, they control email distribution, handle calls, and manage phishing operations, monitoring outcomes in real time and receiving logs containing the stolen data.
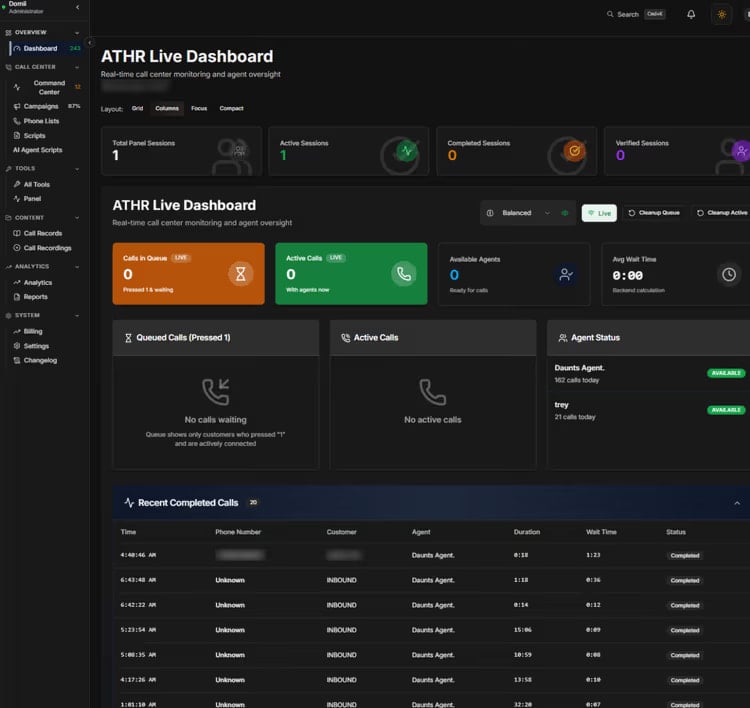
Source: Abnormal
Researchers at Abnormal warn that ATHR significantly reduces the manual effort for the operator and provides threat actors with an integrated platform that can handle all stages of a TOAD attack without the need to configure individual components.
This allows less technical attackers with no infrastructure to deploy automated vishing attacks from start to finish.
"The shift from a fragmented, manually intensive operation to a productized, largely automated one means TOAD attacks no longer require large teams or specialized infrastructure," Abnormal warns.
With the rise of ATHR-like cybercrime platforms, the researchers expect vishing attacks to become more frequent and more difficult to distinguish from legitimate communications.
Defending against such attacks requires a different approach, since the lure emails carry no reliable indicators, are customized to authenticate correctly, and appear as valid notifications.
However, detection is possible by checking the communication behavioral patterns between a sender and a recipient, and identifying if similar lures containing a phone number reached the organization within a short time frame.
Abnormal researchers say that modeling normal communication behavior across the organization can help AI-powered detection flag anomalies before targets make a call.
-
Hackers exploit Marimo flaw to deploy NKAbuse malware from Hugging Face
Hackers are exploiting a critical vulnerability in Marimo reactive Python notebook to deploy a new variant of NKAbuse malware hosted on Hugging Face Spaces.
Bill Toulas April 16, 2026
-
Google expands Gemini AI use to fight malicious ads on its platform
Google says it is increasingly using its Gemini AI models to detect and block harmful ads on its advertising platforms, as scammers and threat actors continue to evolve their tactics to evade detection.
- April 16, 2026
- 11:24 AM
 0
0
Most "AI SOCs" Are Just Faster Triage. That's Not Enough.
AI-powered SOC tools promise automation, but most only speed up triage instead of reducing real workload. Tines shows how real gains come from end-to-end workflows that execute actions across systems, not just summarize alerts.
- April 16, 2026
- 10:02 AM
 0
0
Cisco says critical Webex Services flaw requires customer action
Cisco has released security updates to patch four critical vulnerabilities, including a fixed improper certificate validation flaw in the company's cloud-based Webex Services platform that requires further customer action.
Data breach at edtech giant McGraw Hill affects 13.5 million accounts
The ShinyHunters extortion group has leaked data from 13.5 million McGraw Hill user accounts, stolen after breaching the company's Salesforce environment earlier this month.
- April 16, 2026
- 06:35 AM
 0
0
US nationals behind DPRK IT worker 'laptop farm' sent to prison
Two U.S. nationals have been sent to prison for helping North Korean remote information technology (IT) workers to pose as U.S. residents and get hired by over 100 companies across the country, including many Fortune 500 firms.
- April 16, 2026
- 04:32 AM
 0
0
Microsoft: April Windows Server 2025 update may fail to install
Microsoft is investigating an issue causing this month's KB5082063 security update to fail to install on some Windows Server 2025 systems.
- April 16, 2026
- 03:37 AM
 0
0
Critical Nginx UI auth bypass flaw now actively exploited in the wild
A critical vulnerability in Nginx UI with Model Context Protocol (MCP) support is now being exploited in the wild for full server takeover without authentication.
- April 15, 2026
- 06:35 PM
 1
1
New AgingFly malware used in attacks on Ukraine govt, hospitals
A new malware family named 'AgingFly' has been identified in attacks against local governments and hospitals that steal authentication data from Chromium-based browsers and WhatsApp messenger.
- April 15, 2026
- 05:57 PM
 0
0
WordPress plugin suite hacked to push malware to thousands of sites
More than 30 WordPress plugins in the EssentialPlugin package have been compromised with malicious code that allows unauthorized access to websites running them.
- April 15, 2026
- 04:33 PM
 0
0
Access GPT, Gemini, and Claude in one $30 app to get tasks done faster
Try the ChatOn Premium Plan for one year at $29.99 and see how an all-in-one AI assistant can simplify workflows, boost productivity, and turn ideas into polished content across devices.
- April 15, 2026
- 02:02 PM
 0
0
Signed software abused to deploy antivirus-killing scripts
A digitally signed adware tool has deployed payloads running with SYSTEM privileges that disabled antivirus protections on thousands of endpoints, some in the educational, utilities, government, and healthcare sectors.
- April 15, 2026
- 01:59 PM
 0
0
Microsoft pays $2.3M for cloud and AI flaws at Zero Day Quest
Microsoft has awarded $2.3 million to security researchers after receiving nearly 700 submissions during this year's Zero Day Quest hacking contest.
- April 15, 2026
- 12:20 PM
 0
0
CISA flags Windows Task Host vulnerability as exploited in attacks
CISA warned U.S. government agencies to secure their systems against a Windows Task Host privilege escalation vulnerability that could allow attackers to gain SYSTEM privileges.
- April 15, 2026
- 10:51 AM
 0
0
Rolling Networks: Securing the Transportation Sector
Modern trucks are rolling networks packed with sensors, connectivity, and attack surfaces, creating new cyber risks. NMFTA's Cybersecurity Conference brings industry leaders together to tackle emerging threats in transportation.
- April 15, 2026
- 10:00 AM
 0
0














No comments:
Post a Comment