FBI seizes 13 more domains linked to DDoS-for-hire services
- May 8, 2023
- 04:29 PM
- 0

cyberstress.org seizure banner (DOJ)
The U.S. Justice Department announced today the seizure of 13 more domains linked to DDoS-for-hire platforms, also known as 'booter' or 'stressor' services.
This week's seizures are part of a coordinated international law enforcement effort (known as Operation PowerOFF) to disrupt online platforms allowing anyone to launch massive distributed denial-of-service (DDoS) attacks against any target for the right amount of money.
"As part of an ongoing initiative targeting computer attack 'booter' services, the Justice Department today announced the court-authorized seizure of 13 internet domains associated with these DDoS-for-hire services," the Department of Justice said.
"The seizures this week are the third wave of U.S. law enforcement actions against prominent booter services that allowed paying users to launch powerful distributed denial-of-service, or DDoS, attacks that flood targeted computers with information and prevent them from being able to access the internet."
The FBI also targeted top stresser services in December 2022 when it seized another 48 domains, with ten previously disrupted platforms registering new domains, allowing them to stay online.
"Ten of the 13 domains seized today are reincarnations of services that were seized during a prior sweep in December, which targeted 48 top booter services," the DOJ said.
"For example, one of the domains seized this week – cyberstress.org – appears to be the same service operated under the domain cyberstress.us, which was seized in December."
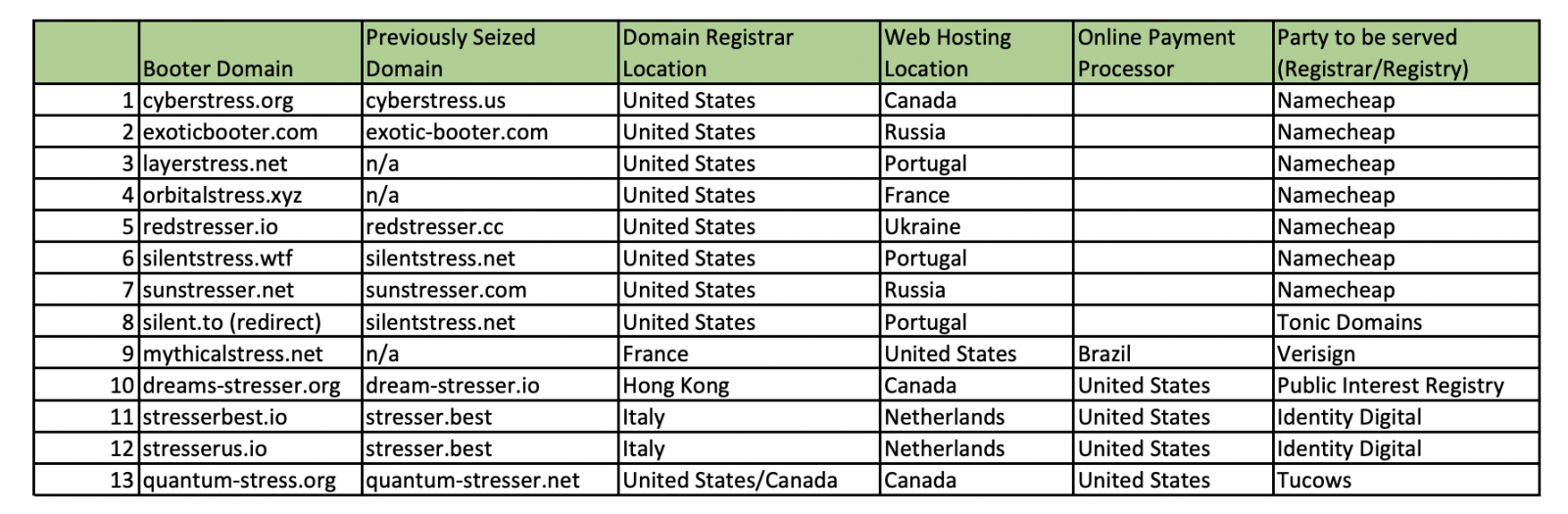
The complete list of domains taken down this week by the FBI and previously seized domains linked to the same operations is embedded below.
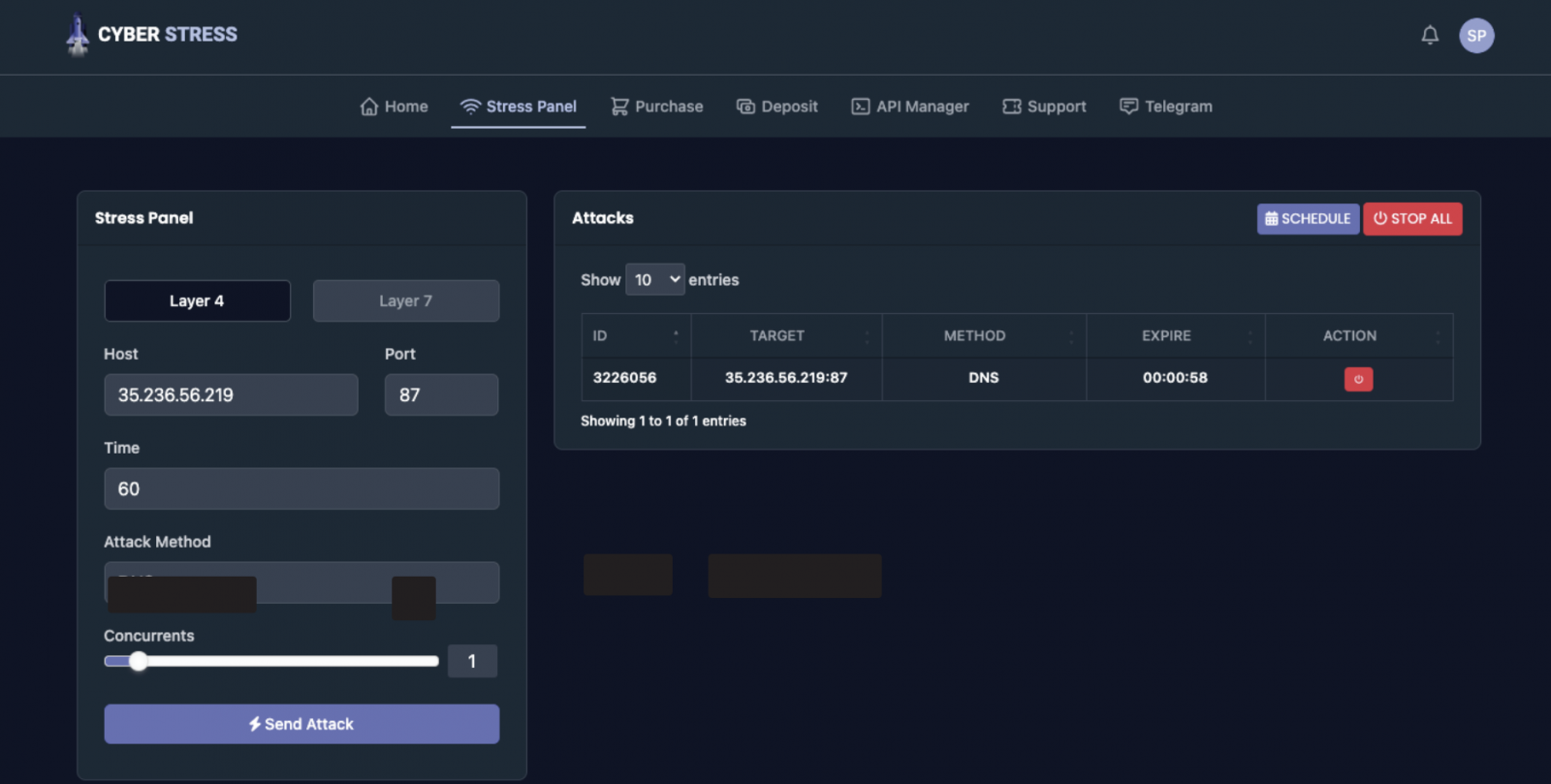
According to the affidavit, the FBI tested the booter services whose domains were seized by opening or renewing accounts with each of them and assessed the effects on target computers via DDoS attacks launched on computers controlled by the agency.
These tests helped confirm the booters' functionality, with the FBI saying that some attacks took the targeted devices offline even though they were using high-capacity Internet connections.
"The FBI tested each of services associated with the SUBJECT DOMAINS, meaning that agents or other personnel visited each of the websites and either used previous login information or registered a new account on the service to conduct attacks," FBI Special Agent Elliott Peterson said.
"I believe that each of the SUBJECT DOMAINS is being used to facilitate the commission of attacks against unwitting victims to prevent the victims from accessing the Internet, to disconnect the victim from or degrade communication with established Internet connections, or to cause other similar damage."
Four defendants charged in late 2022 also pleaded guilty earlier this year to federal charges, admitting that they were either involved in or operated some of the booter services targeted by law enforcement.
The list of defendants and the charges they pleaded guilty to includes:
- Jeremiah Sam Evans Miller, aka "John The Dev," 23, of San Antonio, Texas, admitted on April 6 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named RoyalStresser.com (formerly known as Supremesecurityteam.com);
- Angel Manuel Colon Jr., aka "Anonghost720" and "Anonghost1337," 37, of Belleview, Florida, pleaded guilty on February 13 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named SecurityTeam.io;
- Shamar Shattock, 19, of Margate, Florida, pleaded guilty on March 22 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Astrostress.com; and
- Cory Anthony Palmer, 23, of Lauderhill, Florida, pleaded guilty on February 16 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Booter.sx.
Law enforcement's recent seizures show their commitment to targeting booter service platforms, even though some previously taken down domains have resurfaced."
Feds seize 13 more DDoS-for-hire platforms in ongoing international crackdown
The DDoS whack-a-mole game between law enforcement and miscreants continues.

The US Justice Department has sized the domains of 13 DDoS-for-hire services as part of an ongoing initiative for combatting the Internet menace.
The providers of these illicit services platforms describe them as “booter” or “stressor” services that allow site admins to test the robustness and stability of their infrastructure. Almost, if not all, are patronized by people out to exact revenge on sites they don’t like or to further extortion, bribes, or other forms of graft.
The international law enforcement initiative is known as Operation PowerOFF. In December, federal authorities seized another 48 domains. Ten of them returned with new domains, many that closely resembled their previous names.
"Ten of the 13 domains seized today are reincarnations of services that were seized during a prior sweep in December, which targeted 48 top booter services," the Justice Department said. “For example, one of the domains seized this week—cyberstress.org—appears to be the same service operated under the domain cyberstress.us, which was seized in December. While many of the previously disrupted booter services have not returned, today’s action reflects law enforcement’s commitment to targeting those operators who have chosen to continue their criminal activities.”
According to a seizure warrant filed in federal court, the FBI used live accounts available through the services to take down sites with high-capacity bandwidth that were under FBI control.
"The FBI tested each of the services associated with the SUBJECT DOMAINS, meaning that agents or other personnel visited each of the websites and either used previous login information or registered a new account on the service to conduct attacks," FBI Special Agent Elliott Peterson wrote in the affidavit. "I believe that each of the SUBJECT DOMAINS is being used to facilitate the commission of attacks against unwitting victims to prevent the victims from accessing the Internet, to disconnect the victim from or degrade communication with established Internet connections, or to cause other similar damage."
The Justice Department also said in Monday’s announcement that four of the defendants charged in December pleaded guilty earlier this year. Those defendants and their pleas are:
- Jeremiah Sam Evans Miller, aka “John The Dev,” 23, of San Antonio, Texas, pleaded guilty on April 6 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named RoyalStresser.com (formerly known as Supremesecurityteam.com);
- Angel Manuel Colon Jr., aka “Anonghost720” and “Anonghost1337,” 37, of Belleview, Florida, pleaded guilty on February 13 to conspiracy and violating the computer fraud and abuse act related to the operation of a booter service named SecurityTeam.io;
- Shamar Shattock, 19, of Margate, Florida, pleaded guilty on March 22 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Astrostress.com; and
- Cory Anthony Palmer, 23, of Lauderhill, Florida, pleaded guilty on February 16 to conspiracy to violate the computer fraud and abuse act related to the operation of a booter service known as Booter.sx.
DDoS refers to distributed denial-of-service attacks, in which hundreds of thousands of sites simultaneously direct torrents of junk traffic at a given site to cause it to "deny service" to normal users.

No comments:
Post a Comment