
RORSCHACH – A NEW SOPHISTICATED AND FAST RANSOMWARE
Research by: Jiri Vinopal, Dennis Yarizadeh and Gil Gekker
Key Findings:
- Check Point Research (CPR) and Check Point Incident Response Team (CPIRT) encountered a previously unnamed ransomware strain, we dubbed Rorschach, deployed against a US-based company.
- Rorschach ransomware appears to be unique, sharing no overlaps that could easily attribute it to any known ransomware strain. In addition, it does not bear any kind of branding which is a common practice among ransomware groups.
- The ransomware is partly autonomous, carrying out tasks that are usually manually performed during enterprise-wide ransomware deployment, such as creating a domain group policy (GPO). In the past, similar functionality was linked to LockBit 2.0.
- The ransomware is highly customizable and contains technically unique features, such as the use of direct syscalls, rarely observed in ransomware. Moreover, due to different implementation methods, Rorschach is one of the fastest ransomware observed, by the speed of encryption.
- The ransomware was deployed using DLL side-loading of a Cortex XDR Dump Service Tool, a signed commercial security product, a loading method which is not commonly used to load ransomware. The vulnerability was properly reported to Palo Alto Networks.
Introduction
While responding to a ransomware case against a US-based company, the CPIRT recently came across a unique ransomware strain deployed using a signed component of a commercial security product. Unlike other ransomware cases, the threat actor did not hide behind any alias and appears to have no affiliation to any of the known ransomware groups. Those two facts, rarities in the ransomware ecosystem, piqued CPR interest and prompted us to thoroughly analyze the newly discovered malware.
Throughout its analysis, the new ransomware exhibited unique features. A behavioral analysis of the new ransomware suggests it is partly autonomous, spreading itself automatically when executed on a Domain Controller (DC), while it clears the event logs of the affected machines. In addition, it’s extremely flexible, operating not only based on a built-in configuration but also on numerous optional arguments which allow it to change its behavior according to the operator’s needs. While it seems to have taken inspiration from some of the most infamous ransomware families, it also contains unique functionalities, rarely seen among ransomware, such as the use of direct syscalls.
The ransomware note sent out to the victim was formatted similarly to Yanluowang ransomware notes, although other variants dropped a note that more closely resembled DarkSide ransomware notes (causing some to mistakenly refer to it as DarkSide). Each person who examined the ransomware saw something a little bit different, prompting us to name it after the famous psychological test – Rorschach Ransomware. . ."
READ MORE
New Rorschach ransomware is the fastest encryptor seen so far
Bill Toulas
- April 4, 2023
- 10:13 AM
- 0

Following a cyberattack on a U.S.-based company, malware researchers discovered what appears to be a new ransomware strain with "technically unique features," which they named Rorschach.
Among the capabilities observed is the encryption speed, which, according to tests from the researchers, would make Rorschach the fastest ransomware threat today.
The analysts found that the hackers deployed the malware on the victim network after leveraging a weakness in a threat detection and incident response tool.
Rorschach details
Researchers at cybersecurity company Check Point, responding to an incident at a company in the U.S., found that Rorschach was deployed using the DLL side-loading technique via a signed component in Cortex XDR, the extended detection and response product from Palo Alto Networks.
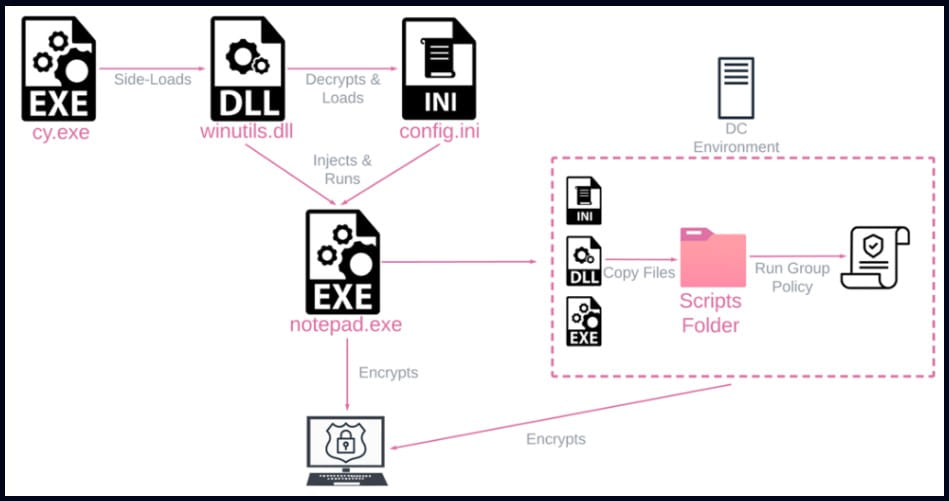
The attacker used the Cortex XDR Dump Service Tool (cy.exe) version 7.3.0.16740 to sideload the Rorschach loader and injector (winutils.dll), which lead to launching the ransomware payload, “config.ini,” into a a Notepad process.
The loader file features UPX-style anti-analysis protection, while the main payload is protected against reverse engineering and detection by virtualizing parts of the code using the VMProtect software.
Check Point reports that Rorschach creates a Group Policy when executed on a Windows Domain Controller to propagate to other hosts on the domain.
After compromising a machine, the malware erases four event logs (Application, Security, System and Windows Powershell) to wipe its trace.
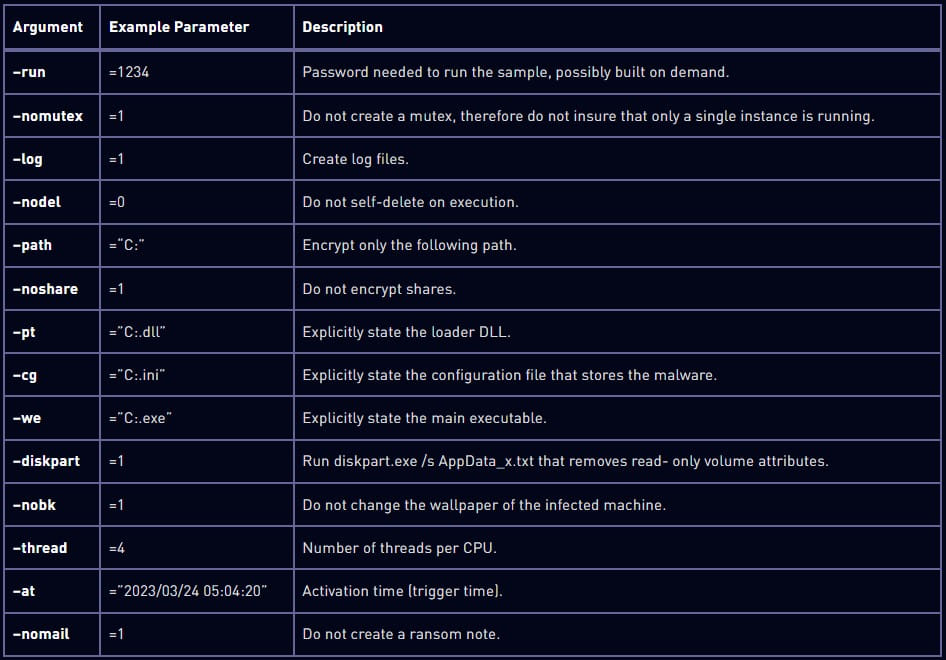
While it comes with hardcoded configuration, Rorschach supports command-line arguments that expand functionality.
Check Point notes that the options are hidden and can't be accessed without reverse engineering the malware. Below are some of the arguments the researchers discovered:
Rorschach's encryption process
Rorschach will start encrypting data only if the victim machine is configured with a language outside the Commonwealth of Independent States (CIS). . .To find how fast Rorschach’s encryption is, Check Point set up a test with 220,000 files on a 6-core CPU machine.
It took Rorschach 4.5 minutes to encrypt the data, whereas LockBit v3.0, considered the fastest ransomware strain, finished in 7 minutes.
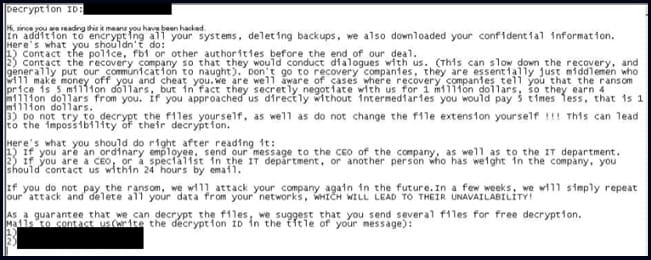
After locking the system, the malware drops a ransom note similar to the format used by the Yanlowang ransomware.
According to the researchers, a previous version of malware used a ransom note similar to what DarkSide used.
Check Point says that this similarity is likely what caused other researchers to mistake a different version of Rorschach with DarkSide, an operation that rebranded to BlackMatter in 2021, and disappeared the same year.
BlackMatter's members alter formed the ALPHV/BlackCat ransomware operation that launched in November 2021.
Check Point assesses that Rorschach has implemented the better features from some of the leading ransomware strains leaked online (Babuk, LockBit v2.0, DarkSide).
Along with the self-propagating capabilities, the malware "raises the bar for ransom attacks."
At the moment the operators of the Rorschach ransomware remain unknown and there is no branding, something that is rarely seen on the ransomware scene."


No comments:
Post a Comment