Ransom Cartel, Reveton ransomware owner arrested, charged in US
Bill Toulas
- August 13, 2024
- 09:33 AM
- 1

The authorities unsealed two separate indictments:
- one for the District of New Jersey regarding the malvertising operation and
- one for the Eastern District of Virginia regarding the Ransom Cartel operation.
An international operation coordinated by the NCA has resulted in the arrest and extradition of a man believed to be one of the world's most prolific Russian-speaking cybercrime actors.
The Ransom Cartel operation
- According to the indictment, Silnikau created and administrated Ransom Cartel, managing the "ransomware-as-a-service" operation and recruiting other cybercriminals from Russian-speaking forums to participate in attacks.
.png)
Source: BleepingComputer
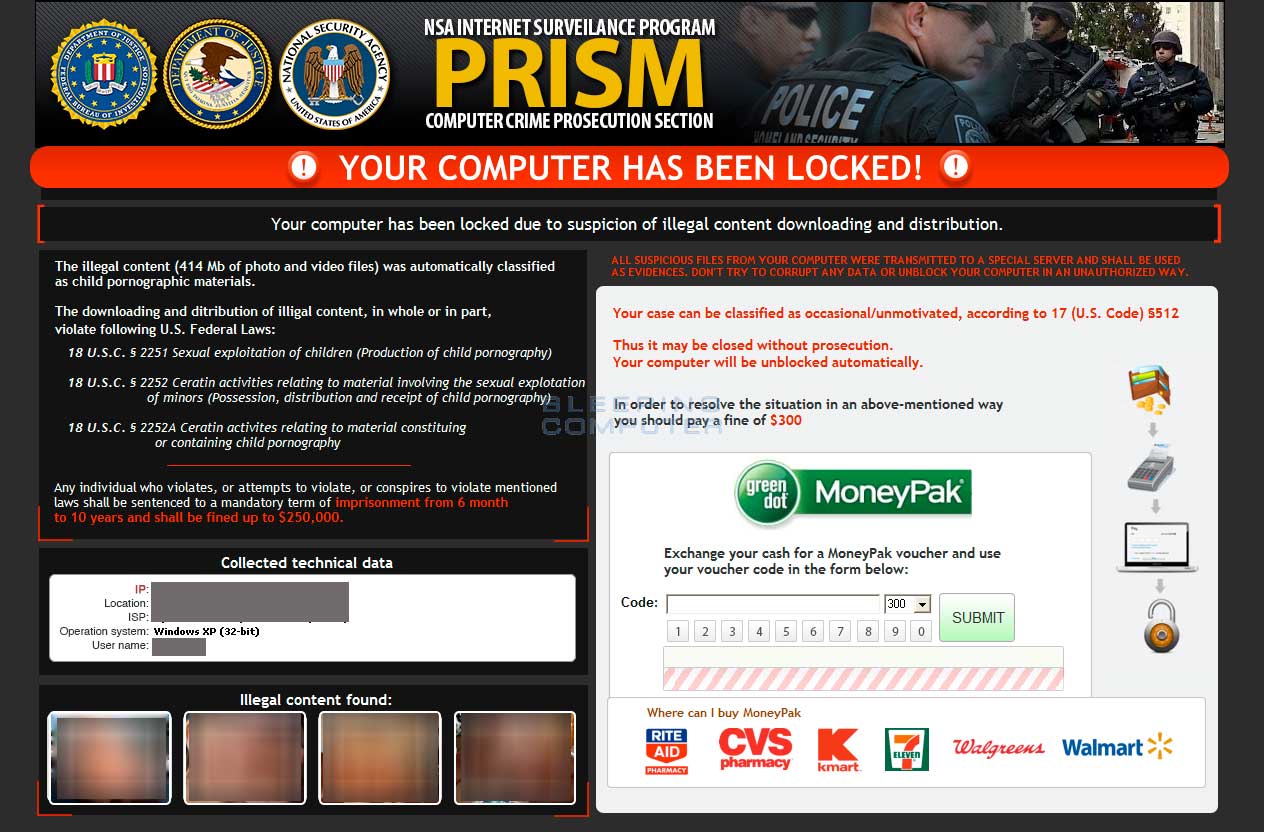
Reveton ransomware
The NCA also states that Silnikau was behind the notorious Reveton trojan, a Windows malware that locked users out of the operating system until a ransom was paid.
Source: BleepingComputer
- Between 2012 and 2014, Reveton was sold to other cybercriminals who heavily distributed it through sites compromised with exploit kits.
- The NCA reports that the Reveton operation generated $400,000 between 2011 and 2013.
Sadly, the malware was so successful that it led to someone taking his and his son's life out of fear that he was going to jail.
Malvertising operation
The defendant is also suspected of orchestrating and executing a large-scale malvertising scheme from October 2013 to March 2022.
- Angler Exploit Kit (AEK): Designed to exploit flaws in web browsers and plugins to deliver additional payloads on the compromised devices.
- Locker malware: A kind of ‘lite’ ransomware tool that prevents the victim from accessing their data, often demanding a payment to restore access.
- Scareware: Deception tools that alleged infections on the victims’ computers via forged alerts, prompting them to download harmful software or provide personal information to the cybercriminals.
Additionally, he collaborated on developing and maintaining technical infrastructure, such as Traffic Distribution Systems (TDSes), to manage and target their malicious campaigns more effectively.
Silnikau could potentially face a sentence exceeding 100 years in prison if convicted on all charges, though the sentencing time is typically much shorter due to the sentences being served concurrently.
-
Russian who sold 300,000 stolen credentials gets 40 months in prison
Georgy Kavzharadze, a 27-year-old Russian national, has been sentenced to 40 months in prison for selling login credentials for over 300,000 accounts on Slilpp, the largest online marketplace of stolen logins, until its seizure in June 2021.
- August 14, 2024
- 07:11 PM
 0
0
-
AutoCanada discloses cyberattack impacting internal IT systems
Hackers targeted AutoCanada in a cyberattack last Sunday that impacted the automobile dealership group's internal IT systems, which may lead to disruptions.
- August 14, 2024
- 12:36 PM
 0
0
-
SolarWinds fixes critical RCE bug affecting all Web Help Desk versions
A critical vulnerability in SolarWinds' Web Help Desk solution for customer support could be exploited to achieve remote code execution, the American business software developer warns in a security advisory today.
- August 14, 2024
- 11:22 AM
 0
0
-
Google says it's focusing on privacy with Gemini AI on Android
Google says it is taking a privacy-minded approach to the integration of AI features like the Gemini assistant on Android devices, implementing end-to-end protection to secure data in transit while keeping the most sensitive data locally on the device.
- August 13, 2024
- 04:47 PM
 1
1
-
X faces GDPR complaints for unauthorized use of data for AI training
European privacy advocate NOYB (None of Your Business) has filed nine GDPR complaints about X using the personal data from over 60 million users in Europe to train "Grok," the social media company's large language model.
- August 12, 2024
- 06:47 PM
 1
1
-
FBI disrupts the Dispossessor ransomware operation, seizes servers
The FBI announced on Monday that it seized the servers and websites of the Radar/Dispossessor ransomware operation following a joint international investigation.
- August 12, 2024
- 05:48 PM
 0
0
-
South Korea says DPRK hackers stole spy plane technical data
South Korea's ruling party, People Power Party (PPP), has issued an announcement stating that North Korean hackers have stolen crucial information about K2 tanks, the country's main battle tank, as well as its "Baekdu" and "Geumgang" spy planes.
- August 12, 2024
- 04:22 PM
 0
0
-
Microsoft is killing the Windows Paint 3D app after 8 years
Microsoft announced that the Paint 3D graphics app will be discontinued later this year and removed from the Microsoft Store in November.
- August 12, 2024
- 03:18 PM
 7
7
-
Hackers posing as Ukraine’s Security Service infect 100 govt PCs
Attackers impersonating the Security Service of Ukraine (SSU) have used malicious spam emails to target and compromise systems belonging to the country's government agencies.
- August 12, 2024
- 02:14 PM
 0
0











No comments:
Post a Comment