The list previously included specific products and companies tied to security concerns, such as Kaspersky, Huawei, ZTE, Hikvision, and Dahua.
FCC bans new routers made outside the USA over security risks
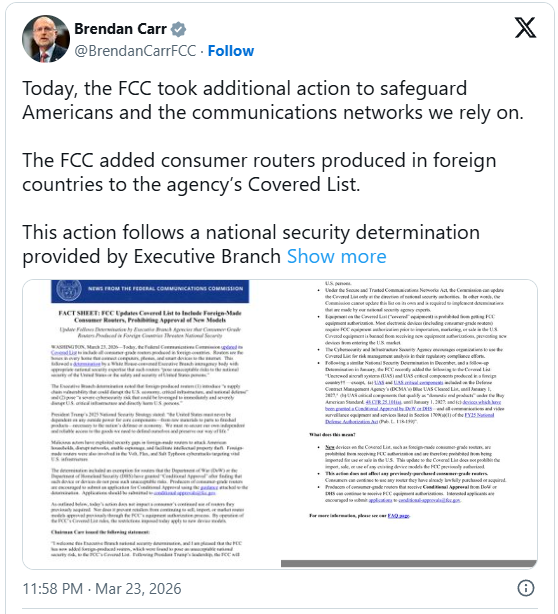
The Federal Communications Commission has updated its Covered List to include all consumer routers made in foreign countries, banning the sale of new models in the U.S.
The Covered List, created under the Secure and Trusted Communications Networks Act of 2019, is an FCC-maintained list of communications equipment and services that the U.S. government has determined to pose an unacceptable risk to national security or the safety of Americans.
The list previously included specific products and companies tied to security concerns, such as Kaspersky, Huawei, ZTE, Hikvision, and Dahua.
Adding all routers manufactured abroad to the Covered List follows a National Security Determination issued on March 20 by an Executive Branch interagency body.
According to the assessment, foreign-produced routers carry a supply-chain risk "that could disrupt the U.S. economy, critical infrastructure, and national defense."
The agency determined that these devices could also be used "to immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons."
In support of the decision, the FCC highlights that foreign-made routers helped the Volt, Flax, and Salt Typhoon hackers carry out attacks that targeted vital U.S. infrastructure.
Exemptions and alternative approval path
Conditional approval has been granted to certain routers used in the U.S. Department of War (DoW) or the Department of Homeland Security (DHS) for drone systems, which have been determined not to constitute a security risk.
Also, the new rules do not bar foreign consumer-grade router makers from seeking approval in the U.S., as long as they transparently disclose:
- Corporate and ownership structure, including any foreign government financial support and influence.
- Manufacturing and supply chain details, including bill of materials, country of origin for all components, IP ownership details, manufacturing and assembly locations, and origin of software/firmware.
- Plan to move critical components manufacturing to the United States, and provide a description of existing U.S.-based manufacturing or assembly processes.
Consumer impact
For regular consumers in the United States, the new rules are expected to have no immediate effect, as all existing routers will continue to be sold in the country.
In what concerns Unmanned Aircraft Systems (UAS) and their critical components, the FCC noted that it will allow software and firmware updates until at least January 1, 2027.
Access to new router models for U.S.-based consumers may become more difficult, and the devices may also become more expensive, as the regulatory approval process adds extra complications and costs.
Given that testing, approvals, and FCC certification typically take a couple of months, even when all conditions are met. In some cases, this might lead to a delay in entering the U.S. market.
Some manufacturers may also decide that the alternative certification pathway is not worth the effort - particularly due to the onshoring requirement - and exit the U.S. market, reducing model availability.
-
Bubble AI app builder abused to steal Microsoft account credentials
Threat actors are evading phishing detection in campaigns targeting Microsoft accounts by abusing the no-code app-building platform Bubble to generate and host malicious web apps.
- March 25, 2026
- 03:48 PM
-
New Torg Grabber infostealer malware targets 728 crypto wallets
A new info-stealing malware called Torg Grabber is stealing sensitive data from 850 browser extensions, more than 700 of them for cryptocurrency wallets.
- March 25, 2026
- 02:32 PM
 0
0
-
New report: How browser-based attacks are bypassing your security controls

Browser-based attacks, from AITM phishing and ClickFix to malicious OAuth apps and session hijacking, are driving today's biggest breaches.
A new report from Push Security breaks down the techniques attackers are using, real-world case studies, and the detection gaps leaving security teams exposed.
-
Stop switching between AI apps—this multi-model tool is just $85
The 1min.AI Advanced Business Plan Lifetime Subscription is available for a one-time payment of $85 (MSRP: $540) through March 29 with code MARCH15. Instead of paying for multiple subscriptions, this setup gives you ongoing access to a range of top AI tools in one place.
- March 25, 2026
- 02:06 PM
 0
0
-
Citrix urges admins to patch NetScaler flaws as soon as possible
Citrix has patched two NetScaler ADC and NetScaler Gateway vulnerabilities, one of which is very similar to the CitrixBleed and CitrixBleed2 flaws exploited in zero-day attacks in recent years.
- March 25, 2026
- 11:52 AM
 0
0
-
Paid AI Accounts Are Now a Hot Underground Commodity
AI accounts are becoming part of the cybercrime supply chain, sold like email accounts or VPS access. Flare Systems shows how underground markets bundle and resell premium AI access at scale.
- March 25, 2026
- 10:02 AM
 0
0
-
Kali Linux 2026.1 released with 8 new tools, new BackTrack mode
Kali Linux 2026.1, the first release of the year, is now available for download, featuring 8 new tools, a theme refresh, and a new BackTrack mode for Kali-Undercover.
- March 25, 2026
- 08:31 AM
 0
0
-
TP-Link warns users to patch critical router auth bypass flaw
TP-Link has patched several vulnerabilities in its Archer NX router series, including a critical-severity flaw that may allow attackers to bypass authentication and upload new firmware.
- March 25, 2026
- 07:11 AM
 2
2
-
Manager of botnet used in ransomware attacks gets 2 years in prison
A Russian national has been sentenced to two years in prison after admitting that the phishing botnet he managed was used to launch BitPaymer ransomware attacks against 72 U.S. companies.
- March 25, 2026
- 04:47 AM
 0
0
-
PTC warns of imminent threat from critical Windchill, FlexPLM RCE bug
PTC Inc. is warning of a critical vulnerability in Windchill and FlexPLM, widely used product lifecycle management (PLM) solutions, that could allow remote code execution.
- March 24, 2026
- 07:04 PM
 0
0
-
Popular LiteLLM PyPI package backdoored to steal credentials, auth tokens
The TeamPCP hacking group continues its supply-chain rampage, now compromising the massively popular "LiteLLM" Python package on PyPI and claiming to have stolen data from hundreds of thousands of devices during the attack.













No comments:
Post a Comment